Infographic - Three steps to stopping advanced email threats
•
1 like•15,801 views
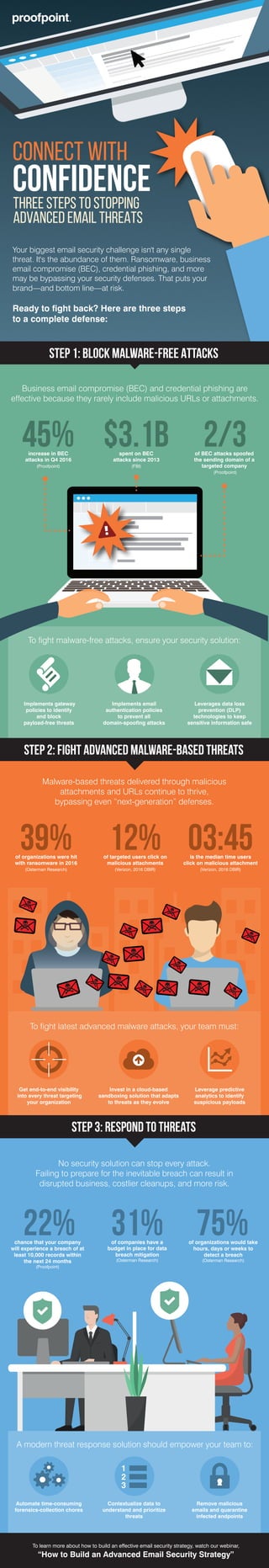
Stop BEC, ransomware and other advanced threats with an advanced email security strategy. Here are three steps to get started.
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
What's hot
What's hot (20)
Verizon Data Breach Investigations Report (DBIR) 2017

Verizon Data Breach Investigations Report (DBIR) 2017
Nonprofit Cybersecurity Readiness - Community IT Innovators Webinar

Nonprofit Cybersecurity Readiness - Community IT Innovators Webinar
Next Dimension and Cisco | Solutions for PIPEDA Compliance

Next Dimension and Cisco | Solutions for PIPEDA Compliance
Containing the outbreak: The healthcare security pandemic

Containing the outbreak: The healthcare security pandemic
Executive Summary of the 2016 Scalar Security Study

Executive Summary of the 2016 Scalar Security Study
Similar to Infographic - Three steps to stopping advanced email threats
Similar to Infographic - Three steps to stopping advanced email threats (20)
Comprehensive Protection and Visibility into Advanced Email Attacks 

Comprehensive Protection and Visibility into Advanced Email Attacks
Balancing Cloud-Based Email Benefits With Security

Balancing Cloud-Based Email Benefits With Security
Overview of Ransomware Solutions from Protection to Detection and Response.pptx

Overview of Ransomware Solutions from Protection to Detection and Response.pptx
Copy of The Ongoing Threat of Ransomware on Small to Medium-Si

Copy of The Ongoing Threat of Ransomware on Small to Medium-Si
Malware Attacks | How To Defend Organizations From It?

Malware Attacks | How To Defend Organizations From It?
Is Cloud the new home for Cyber Criminals? How to be Safe?

Is Cloud the new home for Cyber Criminals? How to be Safe?
Recently uploaded
Recently uploaded (20)
Nell’iperspazio con Rocket: il Framework Web di Rust!

Nell’iperspazio con Rocket: il Framework Web di Rust!
DevoxxFR 2024 Reproducible Builds with Apache Maven

DevoxxFR 2024 Reproducible Builds with Apache Maven
How AI, OpenAI, and ChatGPT impact business and software.

How AI, OpenAI, and ChatGPT impact business and software.
Dev Dives: Streamline document processing with UiPath Studio Web

Dev Dives: Streamline document processing with UiPath Studio Web
Leverage Zilliz Serverless - Up to 50X Saving for Your Vector Storage Cost

Leverage Zilliz Serverless - Up to 50X Saving for Your Vector Storage Cost
WordPress Websites for Engineers: Elevate Your Brand

WordPress Websites for Engineers: Elevate Your Brand
The Ultimate Guide to Choosing WordPress Pros and Cons

The Ultimate Guide to Choosing WordPress Pros and Cons
Ensuring Technical Readiness For Copilot in Microsoft 365

Ensuring Technical Readiness For Copilot in Microsoft 365
DevEX - reference for building teams, processes, and platforms

DevEX - reference for building teams, processes, and platforms
DSPy a system for AI to Write Prompts and Do Fine Tuning

DSPy a system for AI to Write Prompts and Do Fine Tuning
Powerpoint exploring the locations used in television show Time Clash

Powerpoint exploring the locations used in television show Time Clash
Transcript: New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024

Transcript: New from BookNet Canada for 2024: BNC CataList - Tech Forum 2024
Designing IA for AI - Information Architecture Conference 2024

Designing IA for AI - Information Architecture Conference 2024
Unleash Your Potential - Namagunga Girls Coding Club

Unleash Your Potential - Namagunga Girls Coding Club
Infographic - Three steps to stopping advanced email threats
- 1. To learn more about how to build an effective email security strategy, watch our webinar, “How to Build an Advanced Email Security Strategy” Step 2: Fight Advanced Malware-Based Threats Step 3: Respond to Threats Business email compromise (BEC) and credential phishing are effective because they rarely include malicious URLs or attachments. To fight malware-free attacks, ensure your security solution: 2/3of BEC attacks spoofed the sending domain of a targeted company (Proofpoint) Implements gateway policies to identify and block payload-free threats Implements email authentication policies to prevent all domain-spoofing attacks Leverages data loss prevention (DLP) technologies to keep sensitive information safe Malware-based threats delivered through malicious attachments and URLs continue to thrive, bypassing even “next-generation” defenses. No security solution can stop every attack. Failing to prepare for the inevitable breach can result in disrupted business, costlier cleanups, and more risk. 12%of targeted users click on malicious attachments (Verizon, 2016 DBIR) 03:45is the median time users click on malicious attachment (Verizon, 2016 DBIR) To fight latest advanced malware attacks, your team must: Get end-to-end visibility into every threat targeting your organization Invest in a cloud-based sandboxing solution that adapts to threats as they evolve Leverage predictive analytics to identify suspicious payloads chance that your company will experience a breach of at least 10,000 records within the next 24 months (Proofpoint) of companies have a budget in place for data breach mitigation (Osterman Research) of organizations would take hours, days or weeks to detect a breach (Osterman Research) 31% 75%22% A modern threat response solution should empower your team to: Automate time-consuming forensics-collection chores Contextualize data to understand and prioritize threats Remove malicious emails and quarantine infected endpoints Connect WITH CONFIDENCE 45%increase in BEC attacks in Q4 2016 (Proofpoint) 39%of organizations were hit with ransomware in 2016 (Osterman Research) $3.1bspent on BEC attacks since 2013 (FBI) Your biggest email security challenge isn't any single threat. It's the abundance of them. Ransomware, business email compromise (BEC), credential phishing, and more may be bypassing your security defenses. That puts your brand—and bottom line—at risk. Ready to fight back? Here are three steps to a complete defense: Step 1: Block Malware-Free Attacks THREE STEPS TO STOPPING ADVANCED EMAIL THREATS
